1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
| tab1 = [0x0000000000000001, 0x0000000000000003, 0x0000000000000006, 0x0000000000000009, 0x000000000000000A, 0x000000000000000B, 0x000000000000000C, 0x000000000000000D, 0x000000000000000E, 0x000000000000000F, 0x0000000000000010, 0x0000000000000011, 0x0000000000000012, 0x0000000000000014, 0x0000000000000019, 0x000000000000001E, 0x0000000000000028, 0x0000000000000042, 0x0000000000000066, 0x00000000000000A0, 0x0000000000000936, 0x0000000000003D21, 0x00000000000149A7, 0x00000000000243AC, 0x00000000000CB5BE, 0x000000000047DC61, 0x00000000016C0F46, 0x000000000262C432, 0x0000000004ACE299, 0x0000000010FBC92A, 0x00000000329ECDFD, 0x00000000370D7470]
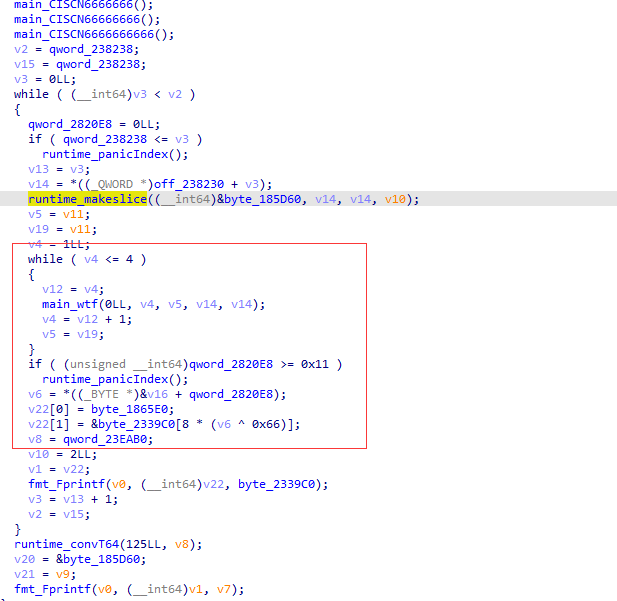
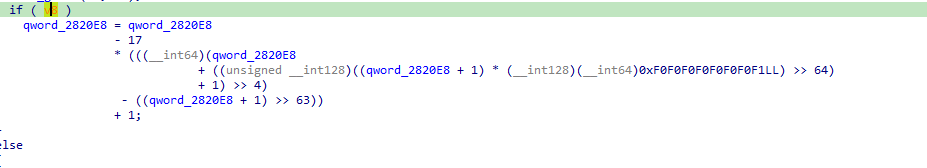
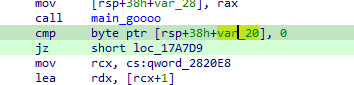
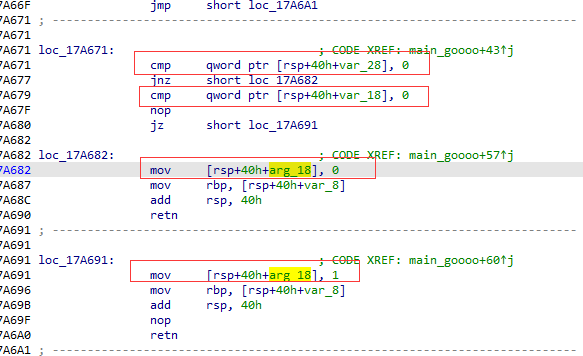
def main_goooo(data):
v4 = [0] * 5
for i in range(len(data)):
v3 = data[i]
v4[v3] ^= 1
return v4[1] == 0 and v4[3] == 0
def main_wtf(a1, a2, a3, a4):
global num
a3[a1] = a2
if a1 == a4 - 1:
if main_goooo(a3):
num = (num + 1) % 17
else:
for i in range(1, 5):
main_wtf(a1+1, i, a3, a4)
def main(N):
global num
num = 0
data = [0] * N
for i in range(1, 5):
main_wtf(0, i, data, N)
print(num)
# 从1开始跑
#flag_i = [main(i) for i in range(1, 16)]
ss = [2, 6, 3, 4, 0, 2, 12, 5]
ss_result = []
for i in range(0x20):
idx = tab1[i]
ss_result.append(ss[((idx-1) % 8)])
print(ss_result)
s1 = [0x54, 0x5e, 0x52, 0x04, 0x55, 0x05, 0x53, 0x5f, 0x50, 0x07, 0x54, 0x56, 0x51, 0x02, 0x03, 0x57]
result2 = ""
for i in range(0x20):
result2 += chr(s1[ss_result[i]] ^ 0x66)
print(result2)
|